Government IT teams face a recurring problem during vendor evaluation: no standardised scoring method. Security teams ask about certifications. Legal teams ask about data residency. Budget officers focus on total cost. Nobody uses the same criteria.
The result is that most digital trust platform comparison exercises produce inconsistent outcomes. Decisions get delayed or made for the wrong reasons. A structured digital trust vendor scorecard removes that inconsistency. It gives IT evaluation committees, CIO staff, and procurement officers a shared framework where every vendor is assessed against the same criteria, with the same evidence requirements, on the same scoring scale.
Let’s discuss the criteria that belong in every trust services evaluation government teams conduct, how to weight them, and what disqualifies a vendor before the contract stage.
Why Government Vendor Evaluations Keep Producing the Wrong Shortlist
Government digital trust services procurement is distinct from standard software buying. The stakes include public records, citizen identity, regulatory accountability, and cross-agency data governance.
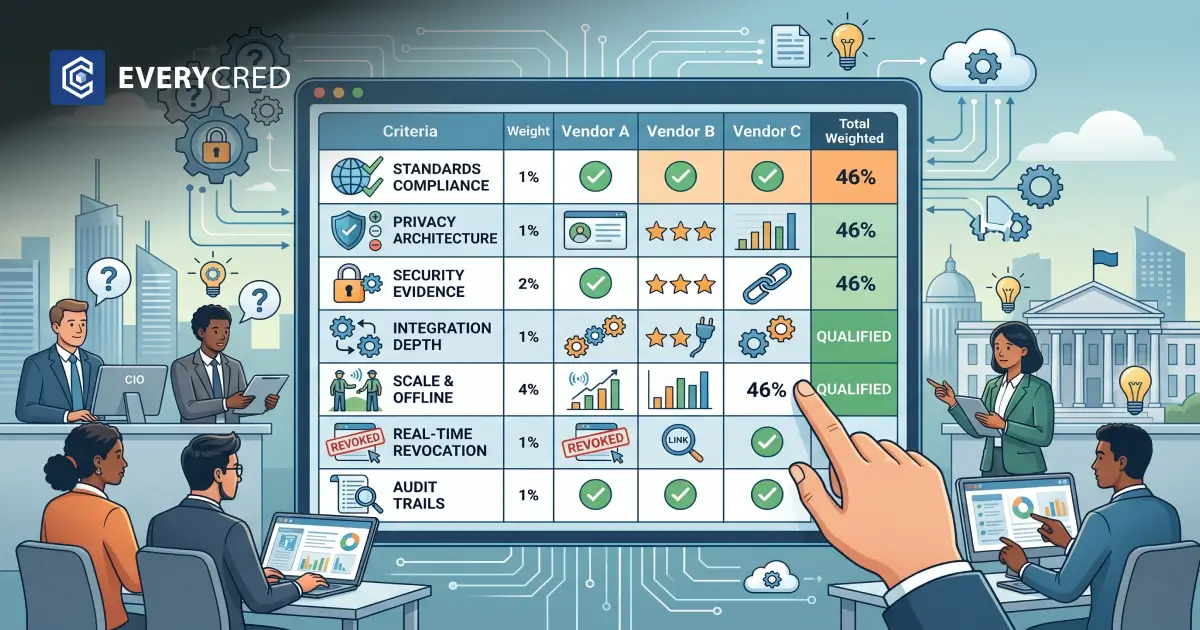
ISACA’s State of Digital Trust 2024 reports that only 46% of government and military sector professionals are confident in the digital trustworthiness of their organisation. That is the lowest figure across all industries surveyed. It reflects a systemic gap in how digital trust services are selected and governed, not just implemented.
A formalised digital trust vendor scorecard is the first structural fix.
Seven Criteria Every Government Scorecard Must Cover
A defensible digital trust platform comparison requires seven distinct evaluation dimensions. Score each on a 0 to 5 scale. Require documented evidence, not verbal confirmation, for every claim.
1. Standards Compliance: The Baseline That Cannot Move
The vendor must build on W3C Verifiable Credentials 2.0, the official W3C Recommendation published in May 2025 and now the global benchmark for cryptographically secure, interoperable digital credentials.
For India, alignment with MeitY’s Digital Personal Data Protection Rules 2025 is mandatory. These rules require encryption, data masking, access controls, and breach notification within 72 hours.
For US federal agencies, NIST SP 800-63-4, published in August 2025, defines Identity Assurance Level (IAL), Authenticator Assurance Level (AAL), and Federation Assurance Level (FAL) as the minimum thresholds for federal digital identity services.
Scorecard question: Can the vendor provide written proof of W3C VC 2.0 alignment and compliance with the applicable national framework?
2. Privacy Architecture Built Into the Product, Not Described in a Document
Require vendors to demonstrate privacy by design in the platform itself. Key scorecard questions:
- How is citizen consent captured, stored, and revoked?
- Can individuals control which data attributes they share per transaction?
- Does the platform support data localisation for state or federal deployments?
India’s DPDP Rules 2025 require verifiable parental consent for minors and continuous auditable governance. A vendor that cannot show these capabilities in its product architecture does not pass this criterion.
3. Security Architecture: Require Evidence, Not Descriptions
During every trust services evaluation government procurement teams conduct, vendors describe security in broad terms. The scorecard enforces specificity. Require:
- Architecture diagrams showing cryptographic signing and blockchain anchoring
- The Decentralised Identifier (DID) method the vendor uses and maintains
- An independent security audit completed within the last 12 months
- A tamper-detection mechanism that works without real-time issuer contact
No third-party audit means no score in this dimension.
4. Integration Depth: The Criterion That Decides Real-World Adoption
A digital trust platform comparison that skips integration depth produces a shortlist that fails in deployment. Government agencies run layered legacy systems. The scorecard must require:
- Full REST API documentation with a pre-purchase sandbox environment
- Demonstrated compatibility with the agency’s existing ERP or case management systems
- Evidence of cross-department credential sharing in a comparable government deployment
EveryCRED’s public sector infrastructure is built on open REST APIs and modular deployment that connects to existing government systems without replacing them.
5. Scale and Offline Capability: Built for Where Government Actually Operates
The trust services evaluation government buyers conduct must include a direct scalability assessment. For India, offline verification is a hard requirement. Field officers in rural districts cannot depend on real-time API calls. Require vendors to demonstrate offline-capable workflows in technical documentation, not in a presentation slide.
For the United States, state and federal programmes serving large populations need volume-tested platforms. Require load test logs.
6. Real-Time Revocation: The Capability That Prevents Post-Issuance Fraud
A credential issued today can become invalid tomorrow. A vendor without instant revocation creates ongoing fraud exposure. The scorecard must ask:
- How quickly does revocation reflect across all verification points after triggering?
- Can back-office systems trigger revocation via API without a manual request?
- Is credential expiry enforced automatically or managed by an administrator?
This criterion is absent from most digital trust vendor scorecard templates, yet it becomes the most operationally critical capability once a programme is live. Understanding how verifiable credentials support public service delivery at scale helps procurement teams ask the right questions here.
7. Audit Trails That Support Accountability, Not Just Logging
Every issuance, verification, and revocation event must be logged in a tamper-proof, queryable format. This is required under India’s DPDP framework and US federal data governance standards. The audit trail must support:
- Real-time compliance dashboards for department administrators
- Export-ready logs formatted for regulatory inspection
- Records that cannot be edited or deleted after creation
How to Build the Scoring Model
Assign weights to the seven criteria based on your agency’s risk profile. A high-volume licensing agency weights revocation and scale more heavily. A ministry managing citizen identity records weights standards compliance and audit trail quality above all else.
The digital trust vendor scorecard produces a total weighted score per vendor, mapping to a tier: qualified, conditional, or disqualified. Conditional gaps move to a remediation checklist with assigned owners and deadlines. EveryCRED’s government credential checklist outlines the technical layer beneath these procurement criteria, useful for IT evaluators structuring their evidence review process.
Responses That Remove a Vendor from the List Immediately
In any digital trust platform comparison, these responses indicate structural problems:
- No documentation of W3C VC 2.0 or national framework compliance
- Security claims backed only by internal testing with no independent audit
- No API sandbox available for pre-procurement technical review
- No reference deployments at a comparable government scale
- Credential revocation managed through a manual support ticket process
One of these warrants clarification. More than two warrants removal from the shortlist.
EveryCRED Scores Against Every Criterion in This Guide
We built EveryCRED to meet the standards this scorecard tests. Our trust credential infrastructure runs on W3C VC 2.0, blockchain-backed cryptographic signing, and real-time revocation with instant propagation across all verification points. Our APIs are open, documented, and available in sandbox environments before any commitment is made.
We have delivered digital trust services for the Government of Maharashtra, Raigad Police, and Navi Mumbai Police, covering credential issuance, field verification, and cross-agency governance at operational scale.
Our platform supports offline verification, data localisation, consent-based sharing, and immutable audit trails that meet India’s DPDP Rules 2025 and align with NIST SP 800-63-4 for US agencies. Our Trust Method provides the DID management and cryptographic governance layer that government evaluators look for in this scorecard.
Schedule a call with our team to walk through how EveryCRED performs against each criterion in your specific procurement context.
FAQs
What is a digital trust services vendor scorecard for government procurement?
A structured tool that helps IT committees score digital trust services vendors against defined, weighted, evidence-based criteria before contract award.
What standards must a digital trust vendor meet for government use?
Vendors must align with W3C VC 2.0, India’s DPDP Rules 2025 for Indian agencies, and NIST SP 800-63-4 for US federal digital identity services.
How does a trust services evaluation for government differ from standard IT procurement?
Government trust services evaluation includes regulatory compliance, citizen data governance, cross-agency interoperability, and accountability requirements that standard procurement does not address.
Why does a digital trust platform comparison fail without a structured scorecard?
Without shared criteria and evidence requirements, evaluators score the same vendor differently, producing unreliable shortlists and avoidable procurement risk.
What is the difference between digital identity and digital trust services?
Digital identity confirms who a person is. Digital trust services govern how credentials are issued, verified, revoked, and audited across government systems.

 12th May, 2026
12th May, 2026