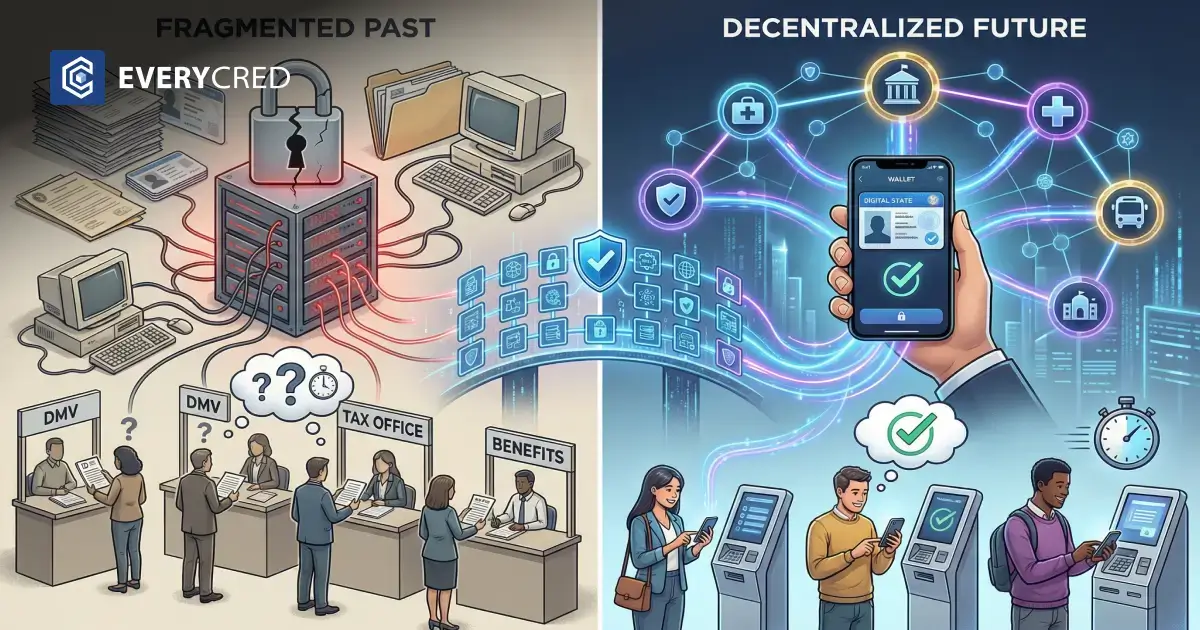
State governments manage millions of citizen interactions every year. Every interaction requires identity verification. Today, that process runs through disconnected systems, paper documents, and manual reviews.
Citizens re-enter the same data for every agency they contact. The result is administrative waste, growing security risk, and poor service delivery at scale.
Digital identity changes that. It replaces physical documents with cryptographically verified credentials that citizens control. Agencies verify identity in seconds. Data moves only when the citizen consents.
America’s Identity Patchwork Is Costing State Governments Billions
As of 2024, only 13 US states offer mobile driver’s licenses (mDLs). There is no national standard for citizen digital identity. The Information Technology and Innovation Foundation describes the current state as an “ad hoc patchwork” where states face interoperability failures and limited practical use cases.
The financial damage from this fragmentation is measurable. The US Government Accountability Office reported $162 billion in improper payments across 68 federal programs in FY2024. Since 2003, cumulative improper payments total $2.8 trillion. Weak identity verification is a documented root cause across multiple program areas.
The digital identity market in government is growing at a CAGR of 18.32% and is projected to reach $16.56 billion by 2035. That growth reflects the scale of the problem and the urgency agencies now feel to address it.
Why Centralized Databases Create Risk Instead of Reducing It
Most state agencies store citizen records in centralized databases. This architecture creates specific, operational problems:
- A single breach exposes records for millions of citizens at once
- Departments store duplicate records with no shared verification layer
- Citizens submit the same personal information multiple times across agencies
- Manual document review cannot reliably detect sophisticated forgeries
Moving to a decentralized identity model eliminates the single point of failure. Data control shifts from the agency’s central server to the citizen’s own device. This means no mass exposure risk when one department is compromised.
The legacy system comparison between digital credential platforms and traditional infrastructure shows clearly why this architectural shift matters for state agencies managing high-volume services.
Decentralized Identity Is How Government Eliminates Fragmented Verification
Decentralized identity gives each citizen a unique, cryptographically verifiable digital credential stored in a secure digital wallet. When a citizen contacts any government agency, the agency requests the credential. The citizen presents it. The system checks the cryptographic signature and confirms validity in milliseconds.
No manual review. No calls to issuing departments. No centralized database lookup.
This works because of published, mature open standards. The W3C published Verifiable Credentials Data Model v2.0 as an official web standard in May 2025. The W3C Decentralized Identifiers (DIDs) v1.1 specification reached candidate recommendation status in 2026. Both are production-ready technical foundations that government agencies can build procurement requirements around with confidence.
Credential verification processes built on these standards are auditable, tamper-evident, and interoperable across departments and jurisdictions.
NIST Just Updated the Rules. Here Is What State Agencies Must Do Now.
The National Institute of Standards and Technology finalized SP 800-63-4, its Digital Identity Guidelines, in August 2025. This revision took four years and incorporated nearly 6,000 public comments. It is the binding technical reference for any US government digital identity implementation.
Key requirements for state agencies under the updated guidelines:
- Apply risk-based assurance levels: Identity Assurance Level (IAL), Authentication Assurance Level (AAL), and Federation Assurance Level (FAL)
- Support citizen-controlled digital wallets within the federation model
- Accommodate multiple identity proofing pathways for equity and accessibility
- Deploy cryptographic verification rather than relying on visual document inspection
Any digital identity platform a state agency procures must align with these requirements. Platforms that do not support NIST-compliant assurance levels create direct compliance exposure.
The National Association of State Chief Information Officers ranks Digital Government and Digital Services at number 3 and Identity and Access Management at number 7 on the 2025 State CIO Top 10 Priorities. Digital identity is not a long-term roadmap item. It is a named, current operational priority at the most senior level of state IT leadership.
The Four-Phase Implementation Plan State CIOs Can Start Today
A full infrastructure replacement is not necessary to get started. A phased approach reduces risk and delivers measurable results at each stage.
Phase 1: Assess Current Infrastructure
- Map all identity touchpoints across departments
- Identify services with the highest manual verification burden
- Define required identity assurance levels by service type
- Document all legacy database dependencies and integration constraints
Phase 2: Run a Controlled Pilot
- Select one bounded use case such as professional licenses or digital employee IDs
- Issue verifiable credentials to a defined test group
- Measure processing time, error rates, and staff time reduction
- Validate revocation and full credential lifecycle management
Phase 3: Integrate with Existing Systems
- Connect the credential issuance engine to existing databases via REST APIs
- Deploy citizen-facing digital wallet applications on major mobile platforms
- Establish cross-department verification protocols
- Train staff on exception handling and citizen support workflows
Phase 4: Scale Across Agencies
- Expand credential issuance to public-facing citizen services
- Build interoperability agreements with other state and federal agencies
- Automate compliance logging and audit trail generation by default
- Extend to high-volume services including benefits enrollment and licensing
The government identity roadmap provides a full technical breakdown of each phase for IT teams preparing deployment plans.
Verifying Once and Trusting Everywhere Is the Strategic Goal
The end state for a state digital identity infrastructure is a model where a citizen verifies identity once and reuses that credential across every agency interaction. A verified credential from the DMV is usable at the benefits office, the tax department, and the permitting authority without re-verification.
This is achievable with current technology. The W3C standards that underpin decentralized identity are designed for cross-system interoperability. Credentials issued under these standards work across any compliant verification system regardless of vendor or platform.
Requirements for cross-agency interoperability:
- Mandate open standards in all technology procurement contracts
- Establish a shared trust framework across departments and state entities
- Retain state control of root cryptographic keys at all times
- Deploy a real-time revocation registry that updates across all integrated verification points
Agencies that address identity-based fraud in benefits programs through verifiable credentials build a reusable verification layer that extends naturally to all other citizen services.
What a Government-Grade Digital Identity Platform Must Deliver
State CIOs evaluating technology for this transition should require specific technical capabilities from any digital identity platform vendor:
- W3C-compliant verifiable credential issuance directly from existing government databases
- Decentralized identity support using standard DID methods
- Real-time credential revocation is visible across all integrated systems
- REST API integration with legacy infrastructure without full system replacement
- Immutable audit logs for compliance reporting and oversight
- Selective disclosure and zero-knowledge proof support to protect citizen privacy
EveryCRED’s digital identity platform is built to meet each of these requirements. It connects directly to existing agency databases through open REST APIs, issues cryptographically signed verifiable credentials to citizen wallets, and supports decentralized identity through its native EVRC DID method. Agencies can issue, manage, and revoke credentials without rebuilding current systems. For state governments evaluating options, the public sector solutions page covers the technical architecture and compliance alignment in detail.
Conclusion
Fragmented citizen identity is an expensive, documented, and solvable problem. The technical standards are finalized. The regulatory framework is clear. The financial case is measurable.
State CIOs who implement a modern digital identity platform will reduce improper payments, close security gaps, and improve service delivery for every citizen who interacts with state government. A phased implementation approach makes this achievable within existing budget cycles and without disrupting current operations.
Digital identity is not an emerging technology. It is an operational requirement that state governments need to act on now.

 2nd April, 2026
2nd April, 2026