Government agencies across the United States and India spend billions every year on manual verification, fraud recovery, and data breach remediation. Most of this spending is preventable. The technology to prevent it, verifiable credentials, already exists as a production-ready web standard. The cost of delaying adoption grows every quarter.
This analysis breaks down the financial damage that credential fraud costs government budgets and shows the verifiable credentials cost-benefit case that decision-makers need to act on now.
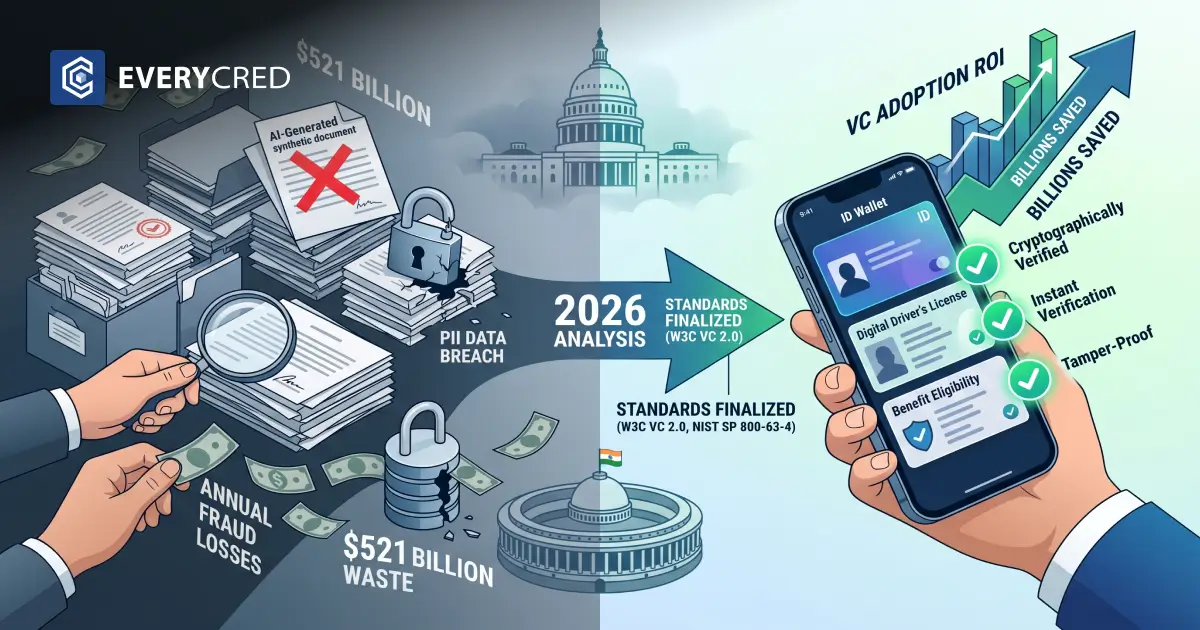
$521 Billion in Annual Fraud Losses and Governments Still Rely on Paper
The U.S. Government Accountability Office estimates annual federal fraud losses between $233 billion and $521 billion. For FY2025, agencies reported $186 billion in improper payments alone. Since 2003, cumulative improper payments have crossed $2.8 trillion.
The root causes remain unchanged:
- Manual document reviews that depend on human judgment
- Siloed databases across federal, state, and local agencies
- Paper-based credentials that are easy to forge and impossible to verify in real time
- No standardized revocation mechanism for expired or fraudulent documents
In India, the Direct Benefit Transfer system saved an estimated ₹3.48 lakh crore by eliminating ghost beneficiaries and duplicate accounts through digital identity verification. PM-KISAN alone removed 2.1 crore ineligible farmers. These savings came from digitizing verification. Verifiable credentials take that same principle further by making every credential cryptographically tamper-proof and instantly verifiable.
The credential fraud cost government agencies absorb today is a direct result of systems that were never designed for the current threat landscape. AI-generated synthetic documents grew 311% between Q1 2024 and Q1 2025. The entry cost for document fraud is now under $30. Every month without credential verification reform, adds to the deficit.
What Government CIOs Lose by Waiting Another Budget Cycle
Delay carries measurable costs across four categories. Understanding these is central to calculating VC adoption ROI accurately.
Fraud and Improper Payments
Federal programs lose 3% to 7% of total obligations to fraud annually. State-administered programs like Medicaid and unemployment insurance are especially vulnerable due to fragmented oversight. Verified credentials eliminate the forgery vector entirely because any alteration to a cryptographically signed credential breaks the signature and fails verification instantly.
Data Breach Exposure
IBM’s 2025 Cost of a Data Breach Report found that the public sector recorded the largest year-over-year increase in breach costs at 10.8%. The U.S. average breach cost hit $10.22 million. Centralized identity databases are high-value targets. Decentralized identity architecture removes the single point of failure by placing credentials on citizens’ own devices rather than in a central repository.
Operational Overhead
Manual identity proofing takes days per applicant. Automated cryptographic verification takes milliseconds. When a government department processes millions of license renewals, permit applications, or benefit eligibility checks per year, the operational savings from verifiable credentials directly improve VC adoption ROI. Staff hours shift from repetitive document checks to higher-value work.
Regulatory Non-Compliance Risk
Two major standards now formally recognize verifiable credentials:
- NIST SP 800-63-4 (final, July 2025) covers digital wallets, verifiable credentials, and mobile driver’s licenses for federal identity systems.
- W3C Verifiable Credentials 2.0 (May 2025) is the global web standard for issuing, holding, and verifying tamper-proof digital credentials.
The EU has mandated Digital Identity Wallets for all 27 member states by December 2026 under eIDAS 2.0. Agencies that delay adoption face rising compliance gaps as these standards become procurement requirements.
The Verifiable Credentials Cost-Benefit Equation in Real Numbers
A practical, verifiable credentials cost benefit analysis for a mid-size government department processing 500,000 credential verifications per year:
- Manual verification cost: $15 to $25 per verification (staff time, cross-agency calls, physical inspection)
- Automated VC verification cost: Under $0.10 per verification (API-based cryptographic check)
- Annual savings on verification alone: $7.4 million to $12.4 million
- Fraud reduction: Conservative 20% reduction in identity-based fraud saves additional millions, depending on program size
- Breach cost avoidance: Decentralized architecture removes the centralized database target, reducing breach probability and the $10.22 million average U.S. breach cost
These numbers make the VC adoption ROI case straightforward. The return appears within the first fiscal year for most agencies. The verifiable credentials cost-benefit ratio improves further when you factor in cross-department interoperability, where one verified credential serves multiple agencies without redundant checks.
Why 2026 Is the Deadline That Cannot Be Pushed Again
Three developments have removed the “wait and see” option:
Standards Are Final
W3C VC 2.0 and NIST SP 800-63-4 are no longer drafts. They are published, production-ready standards. Building on proprietary or legacy formats now means building on a dead end.
Fraud Is Industrialized
AI-generated document forgeries grew 244% in 2025. Fraud-as-a-service platforms sell editable government ID templates for under $30. The credential fraud cost government programs face will only accelerate as generative AI tools improve. Manual inspection cannot keep up.
Global Mandates Are Live
The EU requires EUDI Wallet availability by December 2026. India’s DBT 2.0 phase introduces AI-driven fraud detection with digital identity verification as the backbone. Agencies in the U.S. and India that fall behind these timelines lose interoperability with international counterparts and face audit exposure.
The VC adoption ROI improves the earlier an agency moves. First-mover departments set the verification standards that other agencies must then follow.
How EveryCRED Supports Government Agencies Ready to Act
We built EveryCRED to handle the full credential lifecycle that government operations require: issuance, storage in a secure digital wallet, real-time verification, and instant revocation.
Our platform is already trusted by the Government of Maharashtra, Raigad Police, and Navi Mumbai Police for digital ID credential programs.
What makes our approach practical for government deployment:
- API-first architecture that integrates with existing legacy systems without requiring full IT overhauls
- W3C VC 2.0 and DID v1.1 compliance for long-term standards alignment
- Selective disclosure so citizens share only the data required for each transaction
- Real-time revocation across all verification points when a credential expires or is invalidated
- Immutable audit trails for regulatory accountability and compliance automation
If your agency is evaluating digital trust platforms, we can demonstrate how our infrastructure maps to your verification workflows.
Schedule a demo to see the platform in action.
Conclusion
The credential fraud cost government agencies bear is no longer theoretical. It is $186 billion in reported improper payments, $10.22 million per data breach in the U.S., and a 311% surge in synthetic document fraud. Every quarter of delay adds to the cumulative financial and operational damage.
The standards are final. The threat landscape is accelerating. The verifiable credentials cost-benefit case is backed by data from GAO, NIST, IBM, and real-world deployments across India and the EU. Government CIOs and budget holders who act in 2026 secure measurable VC adoption ROI. Those who wait inherit a growing deficit of trust, security, and fiscal accountability.
FAQs
What is the estimated credential fraud cost government agencies face annually?
The U.S. GAO estimates federal fraud losses between $233 billion and $521 billion annually based on FY2018 to FY2022 data.
How do verifiable credentials reduce government operational costs?
Verifiable credentials replace manual document checks with automated cryptographic verification, cutting per-verification costs from $15 to under $0.10.
Why is 2026 a critical year for VC adoption in government?
NIST SP 800-63-4 and W3C VC 2.0 are now final standards, and the EU mandates digital identity wallets by December 2026.
What is the VC adoption ROI for a mid-size government department?
A department processing 500,000 verifications annually can save $7 million to $12 million in the first year through automation alone.
How does delayed VC adoption increase data breach risk for the government?
Centralized identity databases are primary breach targets, and the public sector saw the largest breach cost increase at 10.8% in 2025.

 5th May, 2026
5th May, 2026