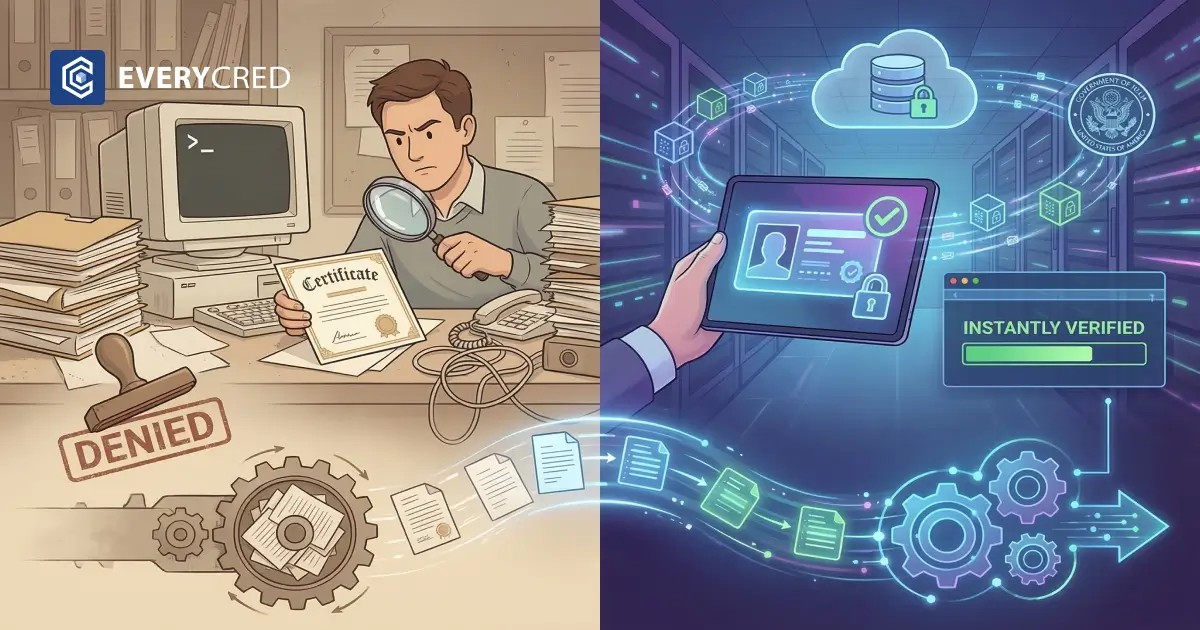
Government agencies process millions of licenses, permits, and employment records annually. Staff members review these documents manually. This manual review creates long processing times and operational backlogs. Government operations teams require automation to process applications faster. They need tools that eliminate paper-based workflows.
The adoption of digital credential software provides this automation. Agencies use this software to issue, manage, and verify records electronically. The transition from physical documents to a digital ID framework improves operational efficiency. It changes how public sector organizations handle data. Implementing credentials verification systems allows agencies to authenticate records instantly. This shift relies on cryptographic proofs rather than human visual inspection.
Why Does Manual Processing Delay Public Services?
Manual workflows rely on human intervention at multiple stages. This reliance introduces delays and increases administrative costs.
- Physical Document Handling: Applicants submit paper documents or scanned copies. Staff members must open, sort, and route these files manually.
- Third-Party Confirmation Calls: Workers telephone issuing institutions to confirm document authenticity. This process depends on the availability and responsiveness of external staff.
- Fragmented Databases: Agencies store records in disconnected systems. Employees must search multiple databases to complete a single credentials verification task.
- Visual Inspection Errors: Staff rely on visual checks to identify forged documents. Sophisticated forgeries often pass visual inspections.
- Data Entry Duplication: Workers manually type applicant information into internal systems. This repetitive task increases the risk of data entry errors.
How Can Automation Improve Government Workflows?
Automation software replaces human tasks with programmed logic. Government agencies use digital verification protocols to authenticate data instantly.
- Instant Cryptographic Checks: Software reads the digital signature on a document. The system confirms authenticity in milliseconds.
- Automated Cross-Referencing: The software queries external registries automatically. Staff members no longer make manual phone calls.
- Self-Service Portals: Applicants upload their verifiable credentials directly to government portals. The system processes the intake without human intervention.
- Standardized Workflows: Automation applies the same rules to every application. This consistency reduces processing variations.
The California Government Operations Agency Blockchain Working Group Report documents how paper-based processes slow down public sector functions. The report identifies cryptographic verification as a practical solution. It recommends these systems to automate employment, education, and licensing checks across state departments.
What Role Do Federal Standards Play in Modernization?
Federal agencies establish guidelines for secure operations. These standards direct how government entities should implement digital ID systems.
Authentication Guidelines
The National Institute of Standards and Technology (NIST) publishes rules for identity systems. The NIST SP 800-63-4 Digital Identity Guidelines specify exact requirements for secure digital verification. Agencies use these guidelines to build compliant IT infrastructure.
Move to Decentralization
NIST guidelines emphasize user-controlled wallets and decentralized identifiers. Agencies must build systems that accept verifiable credentials directly from citizens. This removes the need for centralized government databases holding sensitive physical document scans.
Fraud Prevention
The standards require cryptographic proof of identity. Manual visual checks do not meet the security requirements for high-risk government services. Implementing these standards requires specific software architecture. You can evaluate how secure platforms align with federal mandates by reviewing the EveryCRED Public Sector solutions architecture.
How Does Cryptography Secure Public Records?
Cryptographic systems use mathematics to secure data. This technology makes documents tamper-evident and permanently verifiable.
- Digital Signatures: The issuing agency applies a mathematical code to the document. This code serves as an unforgeable digital signature.
- Tamper Evidence: Any alteration to the document breaks the digital signature. The digital credential software flags altered documents immediately.
- Decentralized Identifiers (DIDs): DIDs link the credential to the specific user. The system uses the DID to prove ownership.
- Zero-Knowledge Proofs: Users prove they meet a requirement without sharing underlying data. A user can prove they hold a valid driver’s license without revealing their home address.
These mechanisms ensure the integrity of the digital ID. Agencies rely on the cryptography instead of trusting the physical appearance of a document.
Are Legacy Systems Compatible with New Technology?
Government operations rely on older, established database systems. Replacing these systems is expensive and disrupts services. Agencies require solutions that integrate with existing infrastructure.
API Integration
Modern digital credential software uses Application Programming Interfaces (APIs). APIs allow the new software to communicate with legacy databases. Developers write code to connect the two systems.
Automated Routing
The API receives the verifiable credentials and routes the data to the correct internal system. The legacy database stores the verified information automatically. Staff do not intervene in the data transfer.
One-Click Verification
Staff access the new tools through simple interfaces. Agencies use tools like the EveryCRED Verifier Portal to execute one-click digital verification without leaving their standard workflow environment.
Incremental Deployment
Agencies deploy the software in specific departments first. This phased approach limits operational risk. IT teams monitor the integration before expanding the software to other divisions.
What Are the Cost Implications of Manual Verification?
Manual processing incurs direct financial costs for government agencies. Operating budgets absorb these expenses annually.
- Labor Costs: Agencies pay staff for hours spent reviewing paper. These hours represent the largest expense in manual processing workflows.
- Storage Expenses: Government offices lease physical space to store paper archives. Maintaining secure, climate-controlled storage facilities requires significant funding.
- Mailing and Courier Fees: Agencies transport physical documents between departments. Postage and courier services add continuous operational costs.
- Compliance Penalties: Processing delays cause agencies to miss statutory deadlines. Missing deadlines triggers financial penalties and audit failures.
Implementing digital verification eliminates these recurring costs. The initial software investment replaces the perpetual costs of paper management.
Read: Digital Identity Platform for Government: How to Choose the Right Solution
How Do Agencies Measure the Return on Investment?
Government operations teams track specific metrics to measure the success of automation. They compare manual baseline data against automated performance.
| Metric | Manual Process Baseline | Automated Process Result |
| Authentication Time | 3 to 14 days | Under 5 seconds |
| Staff Hours per Application | 45 minutes | 2 minutes |
| Forgery Detection Rate | Variable/Low | 100% (Cryptographic) |
| Data Entry Errors | Moderate | Zero (Automated parsing) |
This table demonstrates the quantitative shift. The transition to verifiable credentials yields measurable reductions in processing time and error rates.
What Are the Steps to Implement Digital Verification?
Government operations teams follow a structured process to deploy these systems. They execute specific tasks to modernize their infrastructure.
- Assess Current Workflows: Teams map the existing manual steps. They identify the specific bottlenecks in the current credentials verification process.
- Define Security Requirements: The agency reviews federal guidelines. They establish the necessary security levels for their specific digital ID use cases.
- Select Software Providers: The agency evaluates vendors. They select digital credential software that supports open standards and APIs.
- Configure APIs: IT departments connect the verification software to the agency’s existing databases.
- Pilot Program: The agency tests the system with a small user group. They monitor the system for errors and refine the process.
- Full Deployment: The agency rolls out the system to all users. They provide training to staff on handling system exceptions.
Check: Compliance Automation Software for Government: Buyer’s Evaluation Framework
How Do Decentralized Systems Protect Citizen Privacy?
Privacy is a primary concern for government agencies processing personal data. Traditional databases centralize data. Centralized databases create targets for cyberattacks.
User-Controlled Storage
Citizens store their digital ID on their personal devices. The government does not maintain a massive central repository of these specific files.
Selective Disclosure
Citizens share only the required data fields. If an agency only needs to verify residency status, the citizen does not share their full employment history.
Consent-Based Sharing
The software requires explicit user consent before transmitting data. The system logs these transactions for audit purposes.
No Tracking
Decentralized systems prevent issuing agencies from tracking when and where citizens use their verifiable credentials. The verification happens directly between the citizen and the verifying agency.
Ready to Automate Your Verification Workflows?
Government agencies must process public requests efficiently. Manual checks waste staff hours and delay critical services. Transitioning to automated systems resolves these bottlenecks. EveryCRED provides the infrastructure to modernize these workflows. The platform uses the EVRC DID method and blockchain technology to authenticate records instantly. Agencies use open REST APIs to connect the platform to their current legacy systems. This enables one-click verification without requiring a total IT overhaul. The software ensures all public records, licenses, and identifications remain tamper-proof and fully compliant with data security standards. You can evaluate the technical specifications and schedule a consultation through the EveryCRED contact portal.
Conclusion
Manual processing hinders government efficiency. Employees spend excessive time inspecting paper documents and querying external organizations. Implementing automated credentials verification fundamentally changes public sector operations. Software that reads cryptographic signatures reduces processing times from days to seconds. Agencies integrating modern identification frameworks eliminate visual inspection errors and streamline their databases. The shift toward digital verification architectures allows government operations to scale securely. By prioritizing API-driven integration and cryptographic security, agencies deliver faster, more reliable services to the public.

 16th March, 2026
16th March, 2026