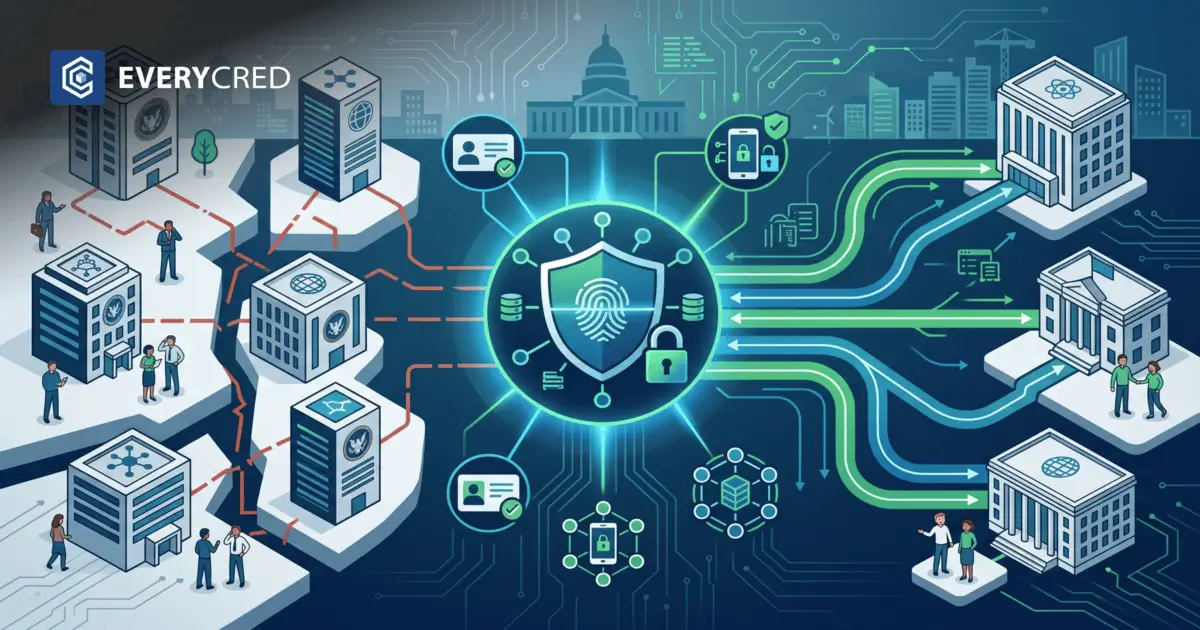
Federal IT leaders manage complex networks across multiple agencies. These networks require secure access protocols for millions of users. Currently, isolated databases prevent uninterrupted data sharing between departments. This creates persistent inter-agency identity issues. Federal agencies need effective digital identity management solutions to resolve these fundamental problems. A modern digital identity platform connects these isolated systems. It provides a standard method to verify users across different government domains.
Implementing these architectures requires careful planning and precise execution. IT departments must evaluate their current security postures objectively. They must identify exactly where data silos cause operational delays and increase administrative overhead. The primary objective is to establish a unified verification protocol. This protocol must function across all federal borders without compromising individual agency security mandates.
Legacy Systems Cause Friction Across Federal Departments
Legacy infrastructure forces each agency to maintain its own independent user database. This approach severely limits operational interoperability. When citizens or federal employees move between departments, they must re-verify their credentials entirely. This duplication wastes administrative resources. It also creates inconsistent user records across the broader government ecosystem.
Data Silos Restrict Operations
Agencies store user data in proprietary, closed formats. A database in one department cannot natively read the database in another department. This structural flaw requires manual data entry to transfer basic information.
Redundant Verification Processes
Users submit the exact same identity documents to multiple departments. Each department processes these documents independently. This repetition increases processing times for standard service requests.
Compliance and Audit Risks
Decentralized auditing becomes practically impossible when systems do not communicate. Administrators struggle to track user access patterns across the entire federal network.
A recent audit on identity verification highlights the severe limitations of current centralized login systems. The report emphasizes the explicit necessity for systems that prevent fraud while allowing data to flow securely between authorized departments. Implementing robust digital identity management solutions addresses these core operational defects. They replace disconnected databases with a standardized, unified verification layer.
Security Standards Dictate New Architectural Frameworks
Federal IT leaders must comply with strict federal security directives. A digital identity platform must meet specific cryptographic and privacy standards. The National Institute of Standards and Technology outlines specific technical guidelines for digital identity risk management. These guidelines mandate high assurance levels for authentication and identity proofing.
Identity Assurance Levels
Agencies must classify access requests based on documented risk. The platform must enforce strict, multi-factor identity proofing for high-risk data access.
Cryptographic Verification
The system must use public key infrastructure to validate user credentials. This ensures the digital proof originates directly from a trusted federal issuer.
Zero Trust Architecture
Agencies must verify every access request regardless of the user location or network. The platform evaluates the user device and network context before granting any access.
Privacy Preservation Protocols
The platform must share only necessary data attributes between departments. It should not transmit a complete user profile for a simple eligibility verification request.
Transitioning to this architecture requires modernizing identity infrastructure across all connected networks. IT leaders must deploy these frameworks systematically to maintain continuous operations.
Interoperability Requires Standardized Credential Formats
Inter-agency identity issues stem directly from incompatible data structures. A digital identity platform solves this problem by using standardized verifiable credentials. These credentials package user claims into a recognizable machine-readable format. Any participating agency can read and verify these claims instantly without connecting to the original issuing database.
Universal Technical Standards
The system uses World Wide Web Consortium standards for verifiable credentials. This implementation ensures global compatibility and prevents proprietary format lock-in.
Secure API Integration
Agencies connect to the identity network via standard REST APIs. This architecture allows existing legacy applications to request and verify credentials natively.
Automated Cryptographic Validation
The platform verifies digital signatures automatically in the background. The receiving agency software checks the cryptographic proof against a public registry.
Revocation Registries
Agencies need a reliable method to invalidate compromised credentials. The platform maintains a decentralized revocation registry. When an agency revokes a credential, the registry updates immediately. Other agencies instantly recognize the credential as invalid.
Efficient Data Processing
This automated approach improves government identity verification speeds significantly. System administrators spend less time manually reviewing physical documents. Users experience fewer administrative delays when requesting services from multiple departments.
Decentralized Networks Protect Federal Data Assets
Centralized databases present high-value targets for cyber attacks. If an attacker breaches a central database, they access millions of user records simultaneously. Decentralized digital identity management solutions distribute this risk across the entire network.
Distributed Ledger Technology
The architecture records credential verification status on a distributed ledger. This design prevents any single point of failure. It creates secure digital trust ecosystems among participating agencies.
Tamper-Evident Records
Agencies can detect any unauthorized modification to a credential immediately. The cryptographic hash of the modified credential will fail the verification check instantly.
Localized Credential Storage
Users store their own credentials securely on local devices or agency-managed digital wallets. The central government server does not hold the actual credential data.
Enhanced System Resilience
If one agency node goes offline due to maintenance or failure, the rest of the verification network continues to function normally. This specific structure provides secure blockchain credentials that protect both citizen privacy and federal data integrity. It builds long-term trust in public services by giving users control over their specific data sharing preferences.
How to Select the Right Enterprise Architecture
Federal IT leaders must evaluate platforms based strictly on their ability to handle high transaction volumes. A government-grade digital identity platform must support millions of simultaneous verifications during peak usage periods.
High Availability Infrastructure
The architecture must provide continuous guaranteed uptime. It requires automated failover mechanisms and redundant server configurations across multiple locations.
Comprehensive Auditing Capabilities
The system must generate immutable logs for every single verification event. These logs must support deep forensic analysis during routine security audits.
Disaster Recovery Protocols
Agencies require strict recovery time objectives. The platform must include automated data backups across geographically separate data centers.
Load Balancing Mechanisms
The system must distribute verification requests evenly across multiple servers. This technical requirement prevents system overloads during sudden spikes in network traffic.
Vendor Lock-in Prevention
The platform must use open industry standards. This requirement allows IT departments to migrate to different infrastructure providers in the future without losing their existing credential data. Evaluating a modern credentialing platform requires testing these specific architectural requirements. IT teams must conduct rigorous load testing before authorizing full deployment.
EveryCRED Provides Infrastructure for Federal Interoperability
Federal IT leaders need highly reliable systems to connect disparate agency networks. We build digital identity management solutions that establish secure, continuous interoperability.
Our digital identity platform uses verifiable credentials to eliminate inter-agency identity issues at the root level. We design our entire architecture to meet rigorous federal security standards and zero-trust requirements. Our system integrates directly with your existing infrastructure via secure APIs. This implementation reduces manual verification workloads significantly. It secures sensitive data transfers between departments.
Contact EveryCRED to discuss your specific agency integration requirements and request a technical demonstration.
Conclusion
Inter-agency data silos reduce operational efficiency and compromise basic security. Adopting standardized digital identity management solutions resolves these deep structural problems. A modern digital identity platform provides the necessary cryptographic security and technical interoperability. Federal agencies must update their infrastructure to support verifiable credentials and zero-trust principles. This architectural shift protects data and streamlines inter-agency communication effectively. Implementing these systems remains a mandatory step for modernizing government networks.
FAQs
What is a digital identity management solution for government?
It is a secure framework enabling agencies to verify, manage, and authenticate citizen identities digitally.
How does a digital identity platform improve inter-agency interoperability?
It uses standardized verifiable credentials and APIs, allowing seamless, secure data sharing across different federal departments.
Why is decentralized identity important for federal IT systems?
Decentralized architectures reduce honeypot risks, giving citizens data control while helping agencies meet strict compliance standards.
What role do verifiable credentials play in multi-agency ecosystems?
They provide cryptographically secure, tamper-proof digital proofs that are instantly verifiable across independent government networks.
How do modern identity solutions resolve government data silos?
By utilizing distributed ledgers and open standards, modern solutions connect isolated databases into unified digital ecosystems.

 27th April, 2026
27th April, 2026